Frictionless threat intelligence for growing teamsSM
Dive right in
See for yourself
![Realtime Register logo]()
Pulsedive provides essential, timely intelligence that drives our proactive abuse monitoring and mitigation efforts. The comprehensive enrichment and ease of integration allows us to transparently work with our network of resellers and users to combat cybercrime with continuous insights. Theo Geurts, Privacy & GRC Officer, Realtime Register
Get results faster
Pulsedive is committed to making all your workflows frictionless, meaning intuitive investigations, seamless deployment, and painless procurement.Enrich with confidence
Run on-demand passive or active scans on IPs, URLs, and domains, or explore our database of threats enriched with MITRE ATT&CK data.Query and pivot freely
Query indicators and threats across almost any data point with boolean logic using our Explore query language. Pivot across results and export in multiple formats.Automate anywhere
Enrich your workflow with Pulsedive data, integrate with SOAR, or export our data in bulk for detection and alerting in your SIEM, Splunk, or other solutions.Integrate with your existing solutions
Many third-party solutions already integrate with Pulsedive out-of-the-box.![Ingalls Information Security logo]()
Time to discovery is critical for effective Security Operations. Pulsedive gives our team the edge when investigating potential cybercrime. Jason Ingalls, CEO, Ingalls Information Security
How cybersecurity professionals use Pulsedive
For Individuals |
|
|---|---|
VisitorAnyone |
Search and view indicators and threats, and stream the latest industry news and events. |
UserFree Account |
Submit indicators, add comments, and export Explore results. |
ProNon-commercial |
View historical screenshots, increase Analyze, Explore, and API limits, and fetch data from third-party integrations right in Pulsedive. Learn More |
For Teams |
|
|---|---|
APICommercial use |
Integrate Pulsedive into your workflows with flexibility. See Docs |
FeedCommercial use |
Bulk export Pulsedive data in CSV format or using STIX/TAXII 2.1. Download Sample |
|
|
A dedicated, cloud-hosted threat intelligence platform with powerful data management capabilties. Learn More |
Dedicated to making threat intelligence better for all
3 (+1) Pulsedive Utilities For Every Security Analyst
Discover three built-in shortcuts designed for any and every security analyst to get the data you need, in the form you want.
Read Blog
Better Together: The Best Cyber Threat Intelligence Events
Our roundup of the best cyber threat intelligence events you won't want to miss. Get the latest on SANS CTI Summit, FIRST, MITRE ATT&CKcon, and more.
Read Blog
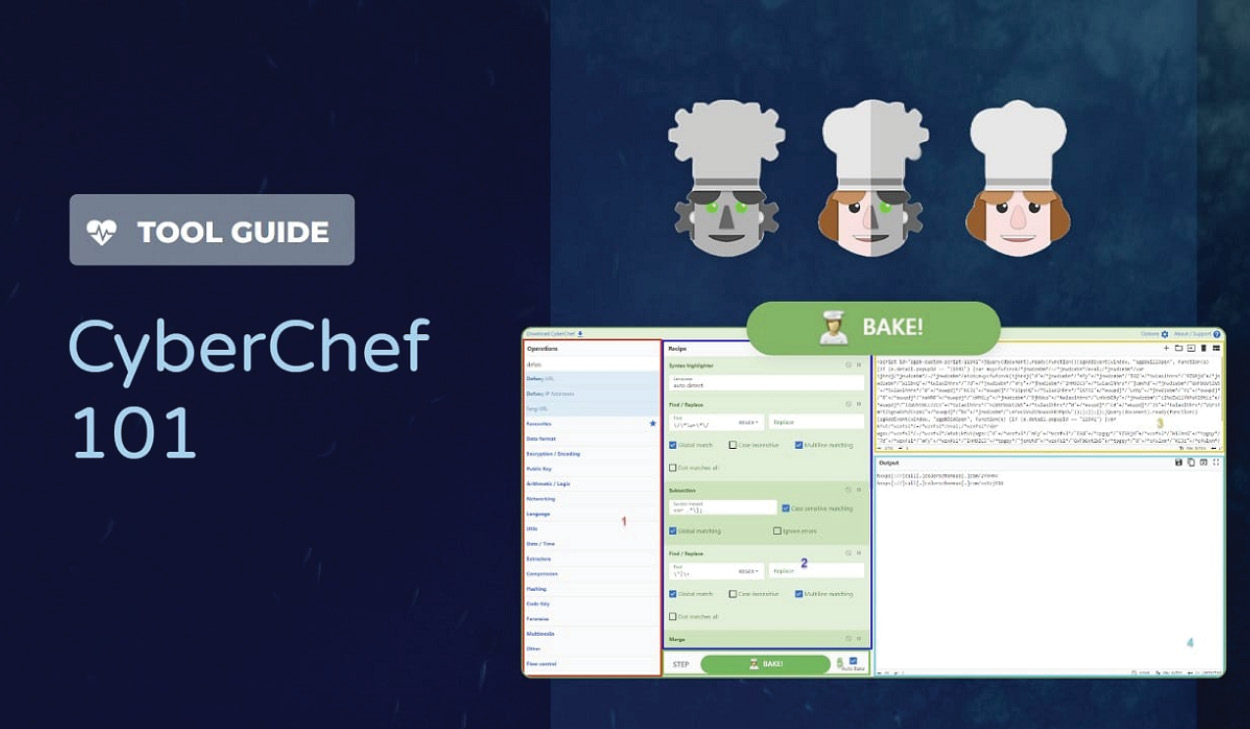
Tool Guide: CyberChef 101
Learn how to use the versatile, open source utility CyberChef. This 101 walks through key operations, a real-world example, and useful resources.
Read Blog
![Pulsedive logo]()
I use Pulsedive every day at work and at home. I love everything about this product and what it has to offer.
Austin H - Information Security Analyst
Join Pulsedive's community of researchers and analysts for free.
3 (+1) Pulsedive Utilities For Every Security Analyst
Discover three built-in shortcuts designed for any and every security analyst to get the data you need, in the form you want. Read BlogBetter Together: The Best Cyber Threat Intelligence Events
Our roundup of the best cyber threat intelligence events you won't want to miss. Get the latest on SANS CTI Summit, FIRST, MITRE ATT&CKcon, and more. Read BlogTool Guide: CyberChef 101
Learn how to use the versatile, open source utility CyberChef. This 101 walks through key operations, a real-world example, and useful resources. Read BlogI use Pulsedive every day at work and at home. I love everything about this product and what it has to offer. Austin H - Information Security Analyst